NMAP, discover devices on the (same) network
There are different tools that can discover devices connected on the same network.
The simpler one is netdiscover.
Let’s check our subnet before. Type, so
ifconfigto discover our ip address and so our subnet
let’s say that our ipaddress is 192.168.1.10
Our subnet is 192.168.1 so all the other device connected on the same subnet are in the following range
192.168.1.0/24 <== it means from 192.168.1.0 to 192.168.1.254
To discover all the other devices connected to the same subnet using netdiscover, type:
netdiscover -r 192.168.1.0/24The result will show you the list of all devices connected:
Currently scanning: Finished! | Screen View: Unique Hosts33 Captured ARP Req/Rep packets, from 12 hosts. Total size: 2094IP At MAC Address Count Len MAC Vendor / Hostname192.168.1.1 e4:8f:34:37:ba:04 20 1200 Vodafone Italia S.p.A.
192.168.1.12 3c:22:fb:b8:8c:c6 1 60 Apple, Inc.
192.168.1.4 5a:92:d0:37:82:da 1 60 Unknown vendor
192.168.1.7 c8:6c:3d:96:65:96 1 174 Amazon Technologies Inc.
192.168.1.6 74:d4:23:c0:e4:88 2 120 Unknown vendor
192.168.1.9 7c:8b:ca:1b:d8:31 1 60 TP-LINK TECHNOLOGIES CO.,LTD.
192.168.1.3 20:f4:78:1c:ed:dc 1 60 Xiaomi Communications Co Ltd
192.168.1.15 7c:8b:ca:1b:d8:31 1 60 TP-LINK TECHNOLOGIES CO.,LTD.
192.168.1.2 80:35:c1:52:d8:e3 1 60 Xiaomi Communications Co Ltd
192.168.1.13 38:1f:8d:ed:70:d2 1 60 Tuya Smart Inc.
192.168.1.11 80:0c:f9:a2:b0:5e 1 60 Amazon Technologies Inc.
192.168.1.124 b8:27:eb:26:8c:04 2 120 Raspberry Pi FoundationThe netdiscover tool can show ipaddress, mac address and the vendor of the device.
A most powerfull tool is nmap
nmap stands for Network MAPping, and is a tool, like netdiscover, that can find devices in your network but will show more information than netdiscover, like open port, services, OS version, …
The visual interface tool for nmap is Zenmap
With Zenmap you can choose graphically which comman on nmap to use.
With Zenmap you can choose different type of scan, for instance, and it basically translate your choose in a nmap command.
For instance, if you choose a °quick scan plus° choise it will execute the command
nmap -sV -T4 -O -F --version-light 192.168.1.1/24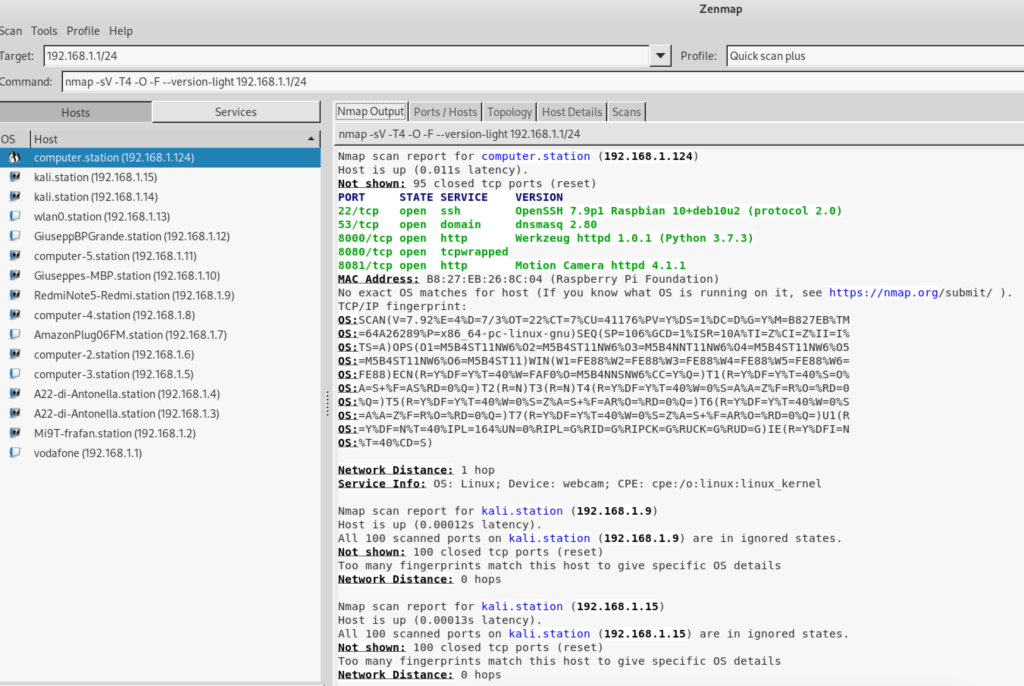
with nmap you can scan a single website or multiple as well, to check port and services exposed
for instance to check google open port and service you can type
nmap google.comDetect firewall
sudo nmap -sA <ipadress>To identify Hostnames
sudo nmap -sL <ipadress>We use “sL” option to find hostnames for the given host by completing a DNS query for each one.